Generate Ssh Key Gitlab Ubuntu
Adding an SSH key to your GitLab account. Now you can copy the SSH key you created to your GitLab account. To do so, follow these steps: Copy your public SSH key to a location that saves information in text format. The following options saves information for ED25519 keys to the clipboard for the noted operating system. However, I have 64 repositories that need to be mirrored across 2 GitLab groups. I can mirror them using a unique ssh key for every repo, but I would find it easier to have 1 ssh key for each group (so 2 of them in my case) so that it would be much easier to maintain. I did not find how to. Jul 29, 2019 Establishing an SSH (Secure Shell) connection is essential to log in and effectively manage a remote server. Encrypted keys are a set of access credentials used to establish a secure connection. This guide will walk you how to generate SSH keys on Ubuntu 18.04. Nov 13, 2017 This New Video shows how to generate SSH keys for GitLab Profile (2017) in user settings, option just above GPG Keys for windows OS using Git Bash GUI. It actually creates a. Then click Help then click Show Ssh Key, then click Generate Key. While you're at it, then copy to the clipboard, and then go to your Gitlab account page and add. This tutorial covers the configuration process of adding SSH key to a GitLab account. Configuration procedure. Before starting the configuration procedure, first generate the SSH key in the target local machine which has to be added to the GitLab account. user1@localhost git$ ssh-keygen -t rsa.
Generate Ssh Key Gitlab
- GitLab Tutorial
- GitLab Basics
- GitLab Users and Groups
- GitLab Issue Tracker
- GitLab Instance Management
- GitLab Continuous Integration
- Selected Reading
Description
The SSH stands for Secure Shell or Secure Socket Shell used for managing the networks, operating systems and configurations and also authenticates to the GitLab server without using username and password each time. You can set the SSH keys to provide a reliable connection between the computer and GitLab. Before generating ssh keygen, you need to have Git installed in your system.
Creating SSH Key
Step 1 − To create SSH key, open the command prompt and enter the command as shown below −
It will prompt for 'Enter file in which to save the key (//.ssh/id_rsa):', just type file name and press enter. Next a prompt to enter password shows 'Enter passphrase (empty for no passphrase):'. Enter some password and press enter. You will see the generated SSH key as shown in the below image −
Generate Ssh Key Gitlab
Step 2 − Now login to your GitLab account and click on the Settings option.
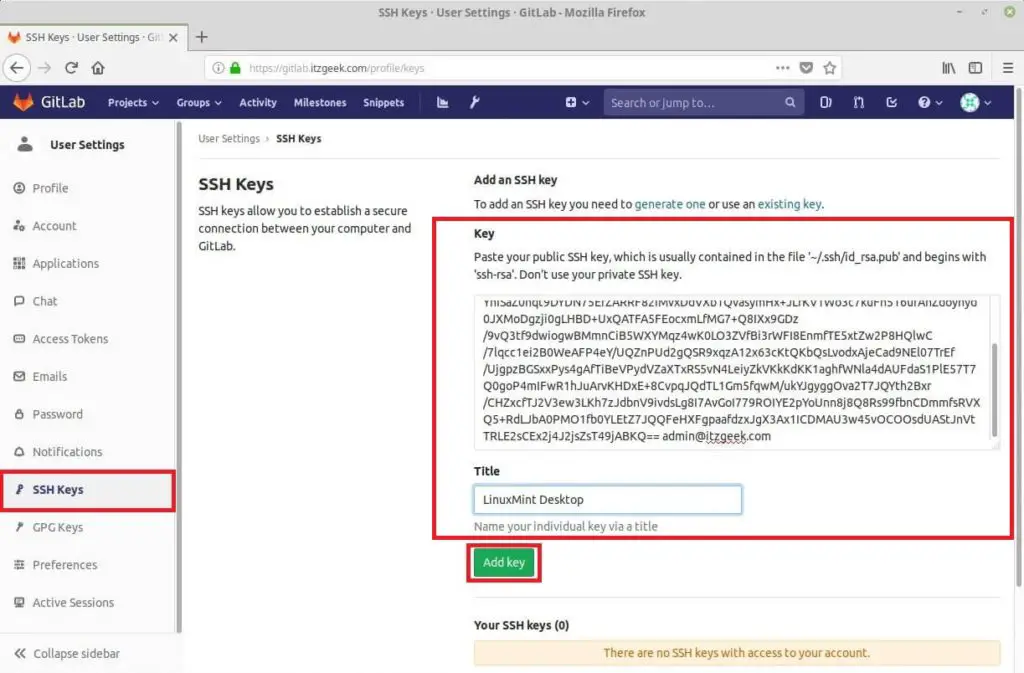
Step 3 − To create SSH key, click on the SSH keys tab at left side of the menu.
Step 4 − Now go to C drive, you will see the file with .pub extension which was generated in the first step.
Step 5 − Next open the key.pub file, copy the SSH key and paste it in the highlighted Key box as shown in the below image −
Step 6 − Click on the Add Key button, to add SSH key to your GitLab. You will see the fingerprint (it is a short version of SSH key), title and created date as shown in the image below −
Introduction
Establishing an SSH (Secure Shell) connection is essential to log in and effectively manage a remote server. Encrypted keys are a set of access credentials used to establish a secure connection.
Generate Ssh Key For Gitlab Ubuntu
This guide will walk you how to generate SSH keys on Ubuntu 18.04. We will also cover setting up SSH key-based authentication to connect to a remote server without requiring a password.
- A server running Ubuntu 18.04
- A user account with sudo privileges
- Access to a terminal window / command line (Ctrl-Alt-T)
If you are already running an Ubuntu 18.04 server, you can skip this step. If you are configuring your server for the first time, you may not have SSH installed.
1. Start by installing the tasksel package:
The system will first ask for confirmation before proceeding:
2. Next, use tasksel to install the ssh-server:
3. Load the SSH server service, and set it to launch at boot:
On your client system – the one you’re using to connect to the server – you need to create a pair of key codes.
To generate a pair of SSH key codes, enter the commands:
/generate-surrogate-key-in-teradata.html. This will create a hidden directory to store your SSH keys, and modify the permissions for that directory. The ssh-keygen command creates a 2048-bit RSA key pair.
For extra security, use RSA4096:
If you’ve already generated a key pair, this will prompt to overwrite them, and those old keys will not work anymore.
The system will ask you to create a passphrase as an added layer of security. Input a memorable passphrase, and press Enter.
This process creates two keys. One is a public key, which you can hand out to anyone – in this case, you’ll save it to the server. The other one is a private key, which you will need to keep secure. The secure private key ensures that you are the only person who can encrypt the data that is decrypted by the public key.
Step 2- Copy Public Key to the Ubuntu Server
First, get the IP address of the Ubuntu server you want to connect to.
In a terminal window, enter:
The system’s IP address is listed in the second entry:
On the client system, use the ssh-copy-id command to copy the identity information to the Ubuntu server:
Replace server_IP with the actual IP address of your server.
If this is the first time you’re connecting to the server, you may see a message that the authenticity of the host cannot be established:
Type yes and press Enter.
The system will check your client system for the id_rsa.pub key that was previously generated. Then it will prompt you to enter the password for the server user account. Type it in (the system won’t display the password), and press Enter.
The system will copy the contents of the ~/.ssh/id_rsa.pub from the client system into the ~/.ssh/authorized_keys directory of the server system.
The system should display:
If your system does not have the ssh-copy-id command, you can copy the key manually over the SSH.
Use the following command:
To log in to a remote server, input the command:
The system should not ask for a password as it is negotiating a secure connection using the SSH keys. If you used a security passphrase, you would be prompted to enter it. After you do so, you are logged in.
If this is the first time you’ve logged into the server, you may see a message similar to the one in part two. It will ask if you are sure you want to connect – type yes and press Enter.
Step 4- Disable Password Authentication
This step creates an added layer of security. If you’re the only person logging into the server, you can disable the password. The server will only accept a login with your private key to match the stored public key.
Edit the sshd_config file:
Search the file and find the PasswordAuthentication option.
Edit the file and change the value to no:
Save the file and exit, then restart the SSH service:
Verify that SSH is still working, before ending the session:
Ssh Generate Key Ubuntu
If everything works, you can close out and resume work normally.
By following the instructions in this tutorial, you have setup SSH-key-based authentication on an Ubuntu 18.04 server.
The connection is now highly secure as it uses a set of unique, encrypted SSH keys.
Next you should also read
Gitlab Create Ssh Key
Learn how to set up SSH key authentication on CentOS to safely communicate with remote servers. Create the…
When establishing a remote connection between a client and a server, a primary concern is ensuring a secure…
Nginx is an open-source server utility designed to work as a reverse proxy, intercepting client requests and…
In this tutorial, Find out How To Use SSH to Connect to a Remote Server in Linux or Windows. Get started with…